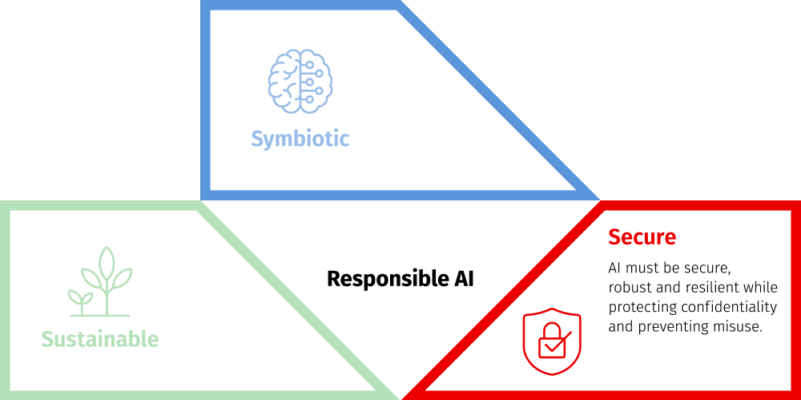
The journey to AI adoption is underpinned by three foundational elements: a symbiotic relationship between humans and machines, robust security measures, and a sustainable approach to accessibility and adaptability. As we embark on the second installment of our three-part series, our focus sharpens on the essence of secure AI. This tenet emphasizes the protection of personal and confidential data, resilience against potential attacks, and the reliable execution of tasks — even in unforeseen scenarios.
Today, traditional cybersecurity threats are intersecting with AI attack vectors, creating a multifaceted threat landscape. This is amplified by the deep integration of AI into critical business processes, which can turn minor vulnerabilities into significant disruptions.
Let’s dive into this second aspect of responsible AI — and see how essential safety principles help create a robust AI ecosystem that ensures optimal performance, data integrity and security.
The essential aspects of secure AI
To establish a secure AI technology environment, organizations must take a holistic approach that includes several critical components, including robust monitoring and observability, stringent identity and access controls, data and integrity protection measures, timely system updates and secure model deployment procedures.
- Monitoring and observability: The cornerstone of a successful AI environment is having a robust monitoring and observability strategy. With the complexity of AI systems, real-time insights into their behavior are paramount. Operational anomalies can have far-reaching consequences, making detection a critical step. By employing advanced monitoring tools, we can proactively identify unusual patterns in data, and model performance and system behavior. This enables rapid responses, minimizing downtime and enhancing the overall stability of the AI environment.
- Identity and access management: In the era of interconnected systems, managing identities and access is crucial. Following the principle of least privilege ensures that individuals have access only to the resources essential to their roles. Implementing a robust identity and access management (IAM) system helps prevent unauthorized access and reduces the risk of data breaches. By assigning granular permissions, organizations can strike a balance between security and operational efficiency, safeguarding sensitive AI-related assets.
- Data privacy and integrity: Data is the lifeblood of AI systems, and strengthening data privacy and integrity is paramount. Encryption at-rest and in-transit provides a strong defense against unauthorized access. By employing encryption mechanisms, we can assure stakeholders that sensitive data remains secure throughout its lifecycle. Also, instituting data integrity provides guarantees that the information used for training and inference remains accurate and untampered, fostering user trust.
- Regular updates and patches: The dynamic landscape of AI frameworks and libraries requires diligent upkeep. Regularly updating and patching software components is not just a maintenance task, but also a security imperative. Vulnerabilities and bugs can expose AI environments to potential threats. By staying up-to-date with the latest releases and security patches, organizations can minimize their attack surface and enhance the resilience of their AI infrastructure.
- Secure model deployment: The deployment phase of AI is a critical point in which security measures must be reinforced. Employing containerization ensures that AI models and their dependencies are encapsulated, mitigating compatibility and security risks. Also, network segmentation isolates AI workloads from other infrastructure components, limiting the potential impact of a breach. By enforcing these practices, organizations can create a secure environment for model deployment while maintaining the overall integrity of their systems.
Charting a path to secure AI
As AI revolutionizes industries, a security model built around mere defensive strategies simply won’t suffice. Businesses need a holistic strategy — one that both safeguards AI infrastructures and prioritizes the buildout of AI solutions with foresight and anticipation of how to counter potential threats.
With the prioritization of monitoring, identity management, data privacy, software maintenance and secure deployments, organizations can confidently navigate the complexities of AI technology. As we stride into the future, let’s embrace these principles. Together, we can unlock the full potential of AI in a landscape of security, sustainability and symbiosis.
To gain the most from a responsible approach to AI, be sure to read the two other articles in this three-part series, including symbiotic AI and sustainable AI.
Download “The Essential Guide to Secure AI” E-book
Your journey to a secure AI begins with finding the best approach to AI integration.